Share this article
Cybercrime is only going to get worse.
The number of new malware variants targeting mobile devices increased by 54% in 2017 (source). And according to Juniper Research, Cybercrime will cost Businesses over 2 trillion dollars worldwide by 2019 (source). These worrying Cybercrime statistics are just two of thousands that you’ll find across the Web.
Cybercrime is a threat to us all.
It is highly likely that your Business will fall victim to a Cyber-attack or breach at some point in its lifecycle. However, there are many preventative steps that you can take to help avoid becoming a victim of Cybercrime.
According to this 2018 Cyber Security breaches survey, seven in ten Businesses (70%) and six in ten of the Charities (63%) that experienced breaches have taken, or are currently taking preventative action in response to their most disruptive breach.
It’s time to fight back!
The below list of essential Cyber Security tips is by no means exhaustive, but it will provide the foundations needed to help you to mitigate the chances of your Business falling victim to a successful Cyber Attack.
Ten essential Cyber Security Tips for protecting your Small Businesses.
Navigate to each tip by clicking on the bookmarks below.
1. Train your staff.
2. Apply Two-factor Authentication (2FA).
3. Get a Firewall.
4. Become Cyber Essentials certified.
5. Enforce Password Management.
6. Use a Password Management app.
7. Good software and systems housekeeping.
8. Backup your data regularly!
9. Create an IT Security policy.
10. Use a VPN for remote access.
1. Train your staff.
Many (if not most) Cyber attacks are successful because of Human error. It only takes a second for a distracted employee to click on a link, or open an attachment that will immediately ruin your day by downloading a malicious file, infecting your entire network, or much worse.
Consider this.
Training your staff on the latest Cyber Security threats and teaching them to be vigilant is JUST as essential as implementing the latest Cyber Security solutions. If you don’t have the skillset in-house, then you’ll find PLENTY of local Cyber Security Consultants that will provide Cyber Security group staff training sessions. If you cannot find a local security consultant, then don’t hesitate to contact us assistance!
2. Apply Two-factor Authentication (2FA).
In this day and age, EVERY Company should be using Two-factor Authentication (2FA) for all critical online applications that are accessed through a user account.
What is 2FA?
2FA is an enhanced security process that requires two separate authentication checks to be completed to confirm your identity before you can access your accounts and services. 2FA adds a second layer of authentication that is required after you have entered your username and password.
Examples of 2FA include a one-time password (OPT) that is sent to you via text message, an automated phone call that provides you with an access code, a dedicated 2FA Smartphone App that generates a one-time code, or even a biometric fingerprint scan.
Most Business Apps include 2FA.
Xero Accounting software, Google’s G-suite and Office 365 are just some of many popular Business apps that include 2FA as an extra layer of account authentication. Although 2FA is usually optional, we strongly recommend using two-factor authentication from day-one.
3. Get a Firewall.
A Firewall protects your Network from unauthorised access, preventing hackers, malware or other malicious attacks from entering your network and ultimately your Systems and Computers. A Firewall will monitor incoming and outgoing traffic activity on your network and decide whether to allow or block this traffic based on the Firewall Configuration rules that have been applied.
Fact.
There is still a surprising number of Small Businesses that don’t have any form of Hardware or Software Firewall in place, yet it’s one of the most effective (and essential) Cyber Security solutions that can be used to maximise your Small Business Network Security. Check out this detailed article ‘What is a Firewall?’ to find out more, including 5 ESSENTIAL reasons to purchase a Hardware Firewall.
4. Become Cyber Essentials certified.
The Cyber Essentials scheme was originally launched by the government back in 2012. The purpose of the scheme was to ensure that Organisations protect themselves against the most common Cyber Attacks by demonstrating a minimum level of Cyber Security.
When becoming Cyber Essentials Certified, your Organisation could prevent up to 80% of Cyber Attacks by applying the following five essential security controls:
- Secure your Internet connection
- Secure your Computer devices and software
- Control access to your data and your services
- Protect yourself from viruses and other malware
- Keep your devices and software up to date
In addition.
The Cyber Essentials Scheme will demonstrate to your clients and shareholders that your Organisation takes Cyber Security VERY seriously and you have taken necessary steps to apply the above essential Cyber Security controls.
Becoming Cyber Essentials isn’t expensive. Check out the IT Governance website to find out more.
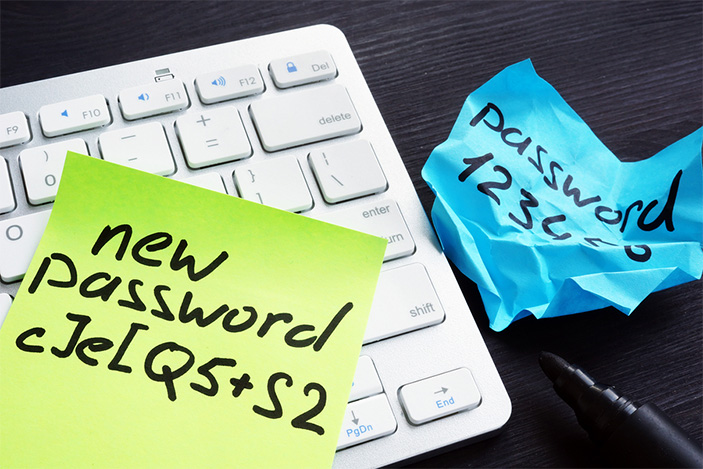
5. Enforce Password Management.
Weak passwords are an easy target for hackers that are seeking to gain unauthorised access to your network. Basic, predictable passwords are probably the biggest security weak spot on your network! Because of this, it is essential to enforce strict password rules within Your Organisation.
For example.
If you use Office 365 Business, then your IT expert or department can create a password expiration policy that forces users to change their password after a set number of days. You can also put password strength rules in place to ensure all newly created passwords contain a minimum number of characters, number and symbols.
In addition.
Sometimes, you won’t be able to directly enforce a strong password policy because your staff will be using external applications that are not directly under your control. Because of this, it is important to educate your staff about the importance of creating strong passwords. Also, make sure that your internal IT Security policy includes guidelines for creating strong passwords.
6. Use a Password Management app.
There are many excellent online password management apps available that can be used to securely store and organise all of your critical account login details. Many of these apps also allow you to log into websites with a single click, saving your staff the headache of copying and pasting their usernames and passwords every time they need to login to a site or application.
In addition.
Password management tools will also discourage users from using the same password for multiple accounts.
If you are looking for a password management tool for your Business, then we highly recommend a solution called 1Password. Visit their website to find out more.
7. Good software and systems housekeeping.
Unfortunately, there is no such thing as a piece of software that is 100% secure. All software applications and operating systems can potentially be exploited by hackers, which is why it’s essential to ensure that any new patches and updates provided by the software developers are installed as soon as they are released.
Important!
Apply automatic updates where possible and if automatic updates cannot be applied, then create a calendar schedule to check for updates and patches for EVERY application you use.
Examples of software to check for updates:
- Operating Systems (Windows, Windows server, OSX etc.)
- Anti-virus/Malware software (Anti-virus definitions typically update automatically, but check your settings to make sure)
- 3rd party applications – such as Microsoft Apps, Adobe Photoshop, accounting software etc.
One advantage of using Cloud-based software Applications (such as Xero, Office 365 G-suite etc.) is that security updates are automatically applied in the background.
Other good housekeeping tips.
Remove pre-installed software from new devices – Many new Computer devices come with software pre-installed. This is sometimes known as “Bloatware” because it is often unnecessary software that you don’t need, or you’ll never use. It is best practice to remove any pre-installed software that you don’t use in order to reduce the number of software vulnerabilities that can be exploited by hackers. Also, pre-installed software will use disk space and memory resources that could potentially slow down your machine.
Apply software security features – Both server and computer operating systems include a number of built in security features that can be applied to control employee access to data by restricting user access and privileges. It is best practice to give users the minimum permissions required to work. It would be unwise to let all of your staff have administrative access to your entire network!
Clean your machines! – Never take it for granted that the devices on your Network are Virus free. It is good practice to run scheduled Anti-virus scans to make sure that no nasty viruses are hiding away in temporary files, or files that your staff may have downloaded from the internet. In addition, it is also good practice to remove temporary files and cookies that could potentially harbour viruses. This can be done manually, or there are a number of utilities available to purchase online that can be used to clean potentially unwanted files from your computers, such as CCleaner for example). NOTE – Cleaning utilities like these should be used with caution. You don’t want to remove any files or registry entries that could stop your computer from working properly!
8. Backup your data regularly!
As previously stated, it is highly likely (almost guaranteed) that your business will become a victim of Cybercrime at some point in its life cycle. In some instances, the only way to recover from a Cyber attack is to restore your critical data and applications. Because of this, it is ESSENTIAL to ensure that your Business has a reliable data backup solution in place.
The future of backup is in the Cloud.
Many Small Businesses backup their Business-Critical data to a physical device, such as an external hard drive, or even optical media. However, backing up your data to a physical device comes with an element of risk. For example, if your backup is being left onsite, then you are at risk of losing your data through a natural disaster or theft. Also, physical media such as tapes and external hard drives have moving parts, which means that they are prone to failure.
A Cloud-based backup service is the most reliable and cost-effective backup solution for start-ups and small businesses. The advantages of using a Cloud backup solution are many. Cloud Backup solutions use data encryption to protect your data from unauthorised access. In addition, your data will be safe in the event of a break-in or natural disaster because it is being backed up at an external location in the Cloud.
It’s important to remember that Cloud Backup services are not the same as Cloud storage. This article clearly explains the difference between the two.
9. Create an IT Security policy.
Businesses of all sizes should have one or more written IT security policies. In order to ensure that everyone is aware of you Organisations IT security policies, processes and responsibilities, it is best practice to include your IT Security policies in your Company new employee welcome pack.
What should a Cyber Security policy include?
Here’s a few content examples:
- Password guidelines (minimum password strength and storage rules)
- Acceptable use guidelines (for Company Email, messaging and internet)
- Remote access guidelines (using a VPN, avoid public networks)
- Mobile device security (This is often detailed in a separate policy)
- Best practice guidelines (think first, click second. If in doubt, don’t open it. Don’t send it, share it. Lock your machine)
- Removable device guidelines (clarify the use of USB sticks, optical media, external hard drives etc.)
This type of policy is often accompanied by a Communications policy and a Social Media usage policy.
10. Use a VPN for remote access.
A VPN (or Virtual Private Network) should be used by all staff that connect to your network from a remote connection. A VPN connection encrypts data that travels to and from your device via a ‘private tunnel’ securing your information from other users that are using the same internet connection.
A piece of advice.
If you are going to invest in a VPN client for your Business, then we strongly advise purchasing a VPN solution from a reputable Organisation, instead of using one of the many free VPN clients that are available on the public domain. Remember, NOTHING is truly free. According to this article, over 38% of free VPN apps contain some sort of malware presence. Isn’t this defeating the object??
Lastly, have you considered outsourcing?
If you don’t have any Cyber Security expertise in-house, or, if you are not big enough to hire an in-house Cyber Security specialist, then why not outsource your IT Security requirements to a Managed Security Services Provider (also known as MSSPs).
An MSSP can provide Cyber Security consultancy and services at a fraction of the cost of employing a full-time IT or network security specialist. A typical portfolio of services provided by an MSSP include:
- Cyber Security solutions implementation – Including multi-factor authentication, Anti-virus and malware protection, VPN implementation, data loss prevention and more.
- Network penetration testing – Solitary or scheduled simulated network attacks that are designed to identify and eliminate security vulnerabilities on your network
- Managed Services – Complex Firewall Management, scheduled updates and patching,
- Cyber Essentials Certification – Onsite Consultancy, policy and process implementation, testing and auditing required to become Cyber Essentials certified.
Conclusion.
Small Businesses that neglect their Cyber Security responsibilities risk going out of Business altogether. If technology is centre to the success of your business, then a respectable level of investment in Cyber Security should ALWAYS be factored into your annual IT budget.